Warning: include_once(site-header.php): failed to open stream: No such file or directory in /home/users/hostsymposium/htdocs/host2019/speakers/RubyLee.php on line 10
Warning: include_once(): Failed opening 'site-header.php' for inclusion (include_path='.:') in /home/users/hostsymposium/htdocs/host2019/speakers/RubyLee.php on line 10
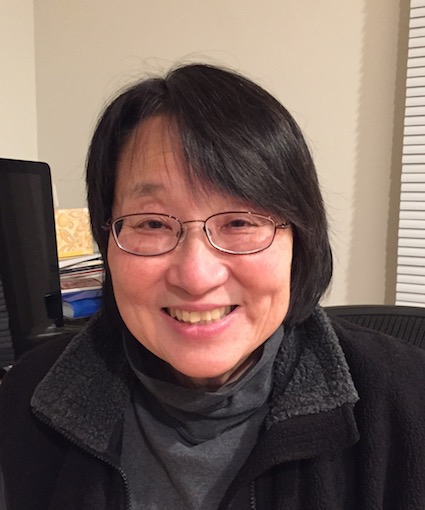
Professor Ruby Lee
Wednesday, May 8th, 2019 | Time: 08:30 - 10:00
Bio: Ruby B. Lee is the Forest G. Hamrick Professor in Engineering and Professor of Electrical Engineering at Princeton University, and the Director of PALMS (Princeton Architecture Lab for Multimedia and Security). Her current research lies at the intersection of Cyber Security, Computer Architecture and Deep Learning. She designs fundamental security features into computer systems, from smartphones to clouds, including secure processors and secure caches that are side-channel resilient. Her team uses deep leaning to improve security, including detecting anomalous behavior in powergrid systems. She also studies improving the security of deep learning systems. Prof. Lee is a Fellow of the ACM and IEEE, has over 130 U.S. and international patents, and numerous publications in computer architecture and computer security conferences. She has served on different National committees to improve cybersecurity research in the U.S. Prior to Princeton, Lee was chief architect at Hewlett Packard, responsible at different times for processor architecture, multimedia architecture and security architecture. She was a founding architect of the PA-RISC processor architecture used in HP’s business, technical and industrial control computer families for decades, and architect of the first multimedia instructions in commercial microprocessors. Her work in security has also been the fore-runner of industry security offerings. Lee has a B.A. (distinction) from Cornell where she was elected a College Scholar, and a PhD in E.E. (minor in C.S.) from Stanford University.Abstract: Performance optimization features in processors can lead to serious security breaches, as exemplified by the recent Spectre, Meltdown and Foreshadow speculative attacks. These transient execution attacks show the vulnerability of processor features to timing attacks, even though they have been correctly designed and verified by existing architecture definitions. In this talk, we suggest that new security design rules need to be added to catch such vulnerabilities at design time or to detect vulnerabilities in existing machines. What are the root causes of speculative attacks and timing attacks? Can we define a small set of security design rules to prevent information leaks and other security breaches due to hardware features? Can we improve performance without degrading security? Can we design hardware architecture that improves security and performance at the same time? What new design strategies and hardware structures can lead to better security? Can we create a tool-chain that can check for potential vulnerabilities at all levels of hardware design? We are entering a new era of security in computer design, with many challenges -- and exciting research opportunities.